A Step by Step Guide to Attack Tree-based Risk Analysis
A "how-to" introduction to assessing risk through attack trees
At first glance, applying attack trees to cyber and physical security may appear challenging. But, in its essence, it is really quite simple. Like most analytic processes, it is possible to go well beyond the basics. However, a lot can be achieved using the fundamentals.
The overall goal of attack tree analysis is to understand how an adversary will behave against a target. Knowing how an adversary will attack allows the defender to create an effective defense.
There are really four key phases of attack tree analysis:
- Create a vulnerability model (attack tree) of the system you wish to protect
- Create profiles describing the adversaries the system faces (e.g., script kiddie, state sponsored agency, disgruntled employee)
- Analyze the vulnerability model in the context of each adversary to determine how they will attack and what impacts will result
- Using the insights gained in the steps above, proposed controls and countermeasures are introduced into the vulnerability model and analysis repeated to gauge their effectiveness).
Vulnerability Attack Tree Model Creation
An attack tree is similar to mathematical trees you are probably already familiar with (such as decision trees). As is customary, the root of the tree is at the top and the tree grows downward toward the bottom-most leaf nodes.
A basic attack tree has three types of nodes: OR, AND and leaf. OR and AND nodes represent logical states an adversary will achieve as they attempt to compromise a system's security.
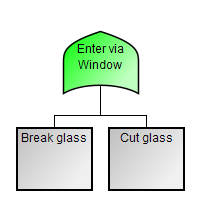 OR nodes
represent
states that
can be realized in a variety of different ways. Each way is represented by one of the
OR node's children. A simple example shows two ways of entering a building via a window (other methods may
exist -
these are shown for simplicity). OR nodes are represented using the traditional Boolean algebra symbol - a
pointy
topped, curved bottom shape (depicted in green).
OR nodes
represent
states that
can be realized in a variety of different ways. Each way is represented by one of the
OR node's children. A simple example shows two ways of entering a building via a window (other methods may
exist -
these are shown for simplicity). OR nodes are represented using the traditional Boolean algebra symbol - a
pointy
topped, curved bottom shape (depicted in green).
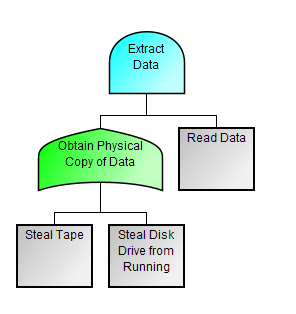 AND nodes
represent
states
that require the attacker to perform multiple steps (represented by the AND node's children). In a classic
attack
tree all of the node's children must be performed. (Sophisticated tools such as Amenaza's SecurITree can capture
more complex relationships, such as m of n). This snippet of a larger attack tree shows the steps an attack
needs to
perform to extract information from a data source (such as a backup tape or disk drive). The attacker must obtain
the data source and then perform whatever technical operation is necessary to Read Data. AND nodes
are
represented by the Boolean shape with a round top and flat bottom (depicted in cyan). Also note how one of the
AND's
children is an OR node with its own children beneath.
AND nodes
represent
states
that require the attacker to perform multiple steps (represented by the AND node's children). In a classic
attack
tree all of the node's children must be performed. (Sophisticated tools such as Amenaza's SecurITree can capture
more complex relationships, such as m of n). This snippet of a larger attack tree shows the steps an attack
needs to
perform to extract information from a data source (such as a backup tape or disk drive). The attacker must obtain
the data source and then perform whatever technical operation is necessary to Read Data. AND nodes
are
represented by the Boolean shape with a round top and flat bottom (depicted in cyan). Also note how one of the
AND's
children is an OR node with its own children beneath.
Leaf nodes are the actual point of interaction between and adversary and their target. These nodes represent the exploit tasks the adversary has to perform. Each of these tasks requires resources from the adversary. The resources may include money, time, skill, physical access and special equipment. An adversary can only perform the leaf level exploits if they possess those resources. The leaf nodes in the examples above are shown as grey rectangles. The activities represented by the leaf nodes differ greatly in the amount and type of resources required. For instance, Steal Tape requires the attacker to have physical access to the data tape, but very little technical ability. Stealing the tape may also expose the attacker to discovery. Once the tape has been stolen, the Read Data step could be done elsewhere. However, reading a backup tape does require access to a potentially expensive tape drive.
Using the AND, OR and Leaf building blocks outlined above, a complete tree is constructed that terminates in a topmost root node. The root node represents the state the attacker wishes to achieve (and that which the defender wants to prevent). Combinations of leaf node events satisfy the AND/OR logic of the tree and form paths to root (which are called attack scenarios).
Of course, not all paths through the tree are equal. The leaf node events associated with the various attack scenarios represent different complexities that the attacker must address. Recognizing this, the analyst defines a variety of indicators that represent the types and amounts of resources the adversary must provide for the leaf level operations, the impacts these activities will have on the defender as higher level AND/OR states are realized, and to assess the benefits that will accrue to the adversary. The latter provide an indication of the attacker's degree of motivation.
Define Threat Agent (Adversarial) Profiles
Based on intelligence information, and reasonable assumptions, the analyst then defines profiles for each type of adversary that may plausibly be interested in the target. Although it may be possible to precisely identify the characteristics of any particular attacker, it is possible to come up with reasonable generalizations for the class of attackers. For instance, Script Kiddies (typically adolescents with minimal formal training) will generally have a low technical ability and little money, but significant time on their hands to perform attacks. They may also be quite bold and brazen because they fail to recognize the potentially serious consequences of their actions. By contrast, a commercial criminal may have significant technical skills and tens of thousands of dollars to fund an attack. However, their attacks will be carefully chosen to avoid detection, and especially, attribution. They understand the risks they face. The two groups also differ in objectives. The script kiddie may simply be looking to deface a website for purposes of recognition and infamy. The commercial criminal may be after valuable intellectual property.
Predict How Each Attacker is Likely to Attack the Target
Evaluate all of the attack scenarios through the tree to understand each path's characteristics in terms of resource requirements, benefits to the attacker and detriments to the victim. Compare each path's characteristics to each of the attack profiles generated previously. Identify the attack scenarios that are feasible and (for each adversary) desirable. Scenarios that are both feasible and desirable are probable. The scenarios that are probably and that will create a significant impact to the victim present risk. At this point, the system operator must determine whether they will accept the level of risk, transfer the risk (perhaps via insurance) or mitigate the risk.
Propose and Test Controls to Mitigate Attack Scenario Risk
If the decision is made to prevent high risk attack scenarios from occurring, the defender needs to identify defensive strategies. In physical situations, this may require physical controls (guns, guards, gates). In cyber situations, it may require techniques such as network segmentation, encryption, authentication and authorization mechanisms. Each of these controls can be incorporated into the original attack tree model and analysis repeated to determine whether the countermeasure is effective. This avoids implementing costly controls which may turn out to be ineffective.
The Need for Software Tools
In principle, all of the steps above can be performed manually. However, this is usually not practical. A typical attack tree may incorporate over a hundred thousand attack scenarios and face a handful of distinct adversaries. This would require an analyst to manually evaluate and compare a half million or more situations.
Fortunately, Amenaza's SecurITree makes the attack tree analysis process simple and easy. Additionally, it incorporates many advanced analytic functions not described above. These identify the critical paths through the tree and help analysts construct effective and cost effective solutions.
The Need for Training
Although the basics of attack tree analysis are straightforward, the maximum benefit of the process (and SecurITree) can be obtained most quickly by taking Amenaza's three-day course on advanced attack tree analysis (usually taught at the customer's site). Also consider the reference white paper on attack tree analysis.


