Introduction to SecurITree
Amenaza Technologies Limited
https://www.amenaza.com
What is SecurITree?
SecurITree is a graphical analysis program, which eases in the creation and interpretation of attack trees. Attack trees represent a logical set of actions which an adversary needs to perform to attack a particular asset, whether it be a critical database server, a nuclear power plant, or electrical transmission wires.
SecurITree is not an automated scanning tool or a magic box which can create answers out of nothing. SecurITree models are created from information you have about your system and its adversaries. SecurITree organizes this information in such a way that it is possible to see through the seemingly intractable complexity of the problem. Through the use of mathematical logic, SecurITree can deduce how an adversary will act against a system and what damage will result. The conclusions will be as sound as the data upon which they are based. The logic used to derive the conclusions is transparent and can be used to communicate with and persuade stakeholders (who may not possess technical expertise) to take appropriate actions.
What is SecurITree?
In addition to predicting what types of attacks will be carried out against an asset, SecurITree can be used to test the efficacy of proposed countermeasures -- before they are constructed. The strength of various defenses can be easily compared.
In order to effectively use SecurITree, you need to understand the concepts it is based on. This demonstration will introduce you to the SecurITree risk analysis approach.
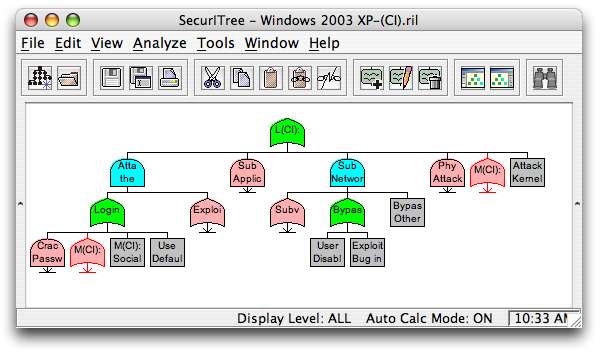
Let us begin by reviewing the SecurITree main screen and examining the building blocks of a SecurITree attack tree model.
SecurITree Window Functions
The main SecurITree window is much like any other program that you may be familiar with. You will see all the familiar menu options such as Save, Load, Print, etc.
In the central, white portion of the window, you can see a 'tree', comprised of multiple colored 'nodes'.
SecurITree Node Functions - What is a node?
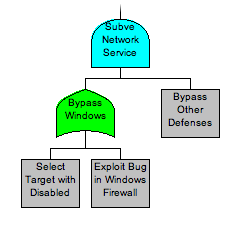
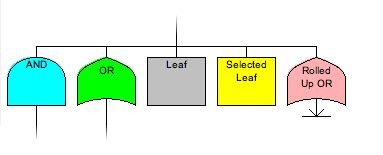
There are two main types of nodes: leaf nodes, and non-leaf nodes. Leaf nodes, represented by a gray rectangle, represent actions which an attacker must do when attacking a system. Leaf nodes are always at the very bottom of the tree, and cannot have any other nodes beneath them.
Non-leaf nodes represent logical states that an attacker may be in after performing one or more of the actions described by child leaf nodes. There are two main types of non-leaf nodes: AND nodes, and OR nodes. AND nodes are used when the attacker must perform all of the sub-attacks beneath the AND node (logical AND). OR nodes are used when the attacker can choose one out of a number of different attacks.
SecurITree Node Functions - Node Shape and Color
You can easily determine what type of node you are looking at by its shape. AND nodes are shown using the boolean AND gate symbol; OR nodes likewise use the boolean OR symbol; Leaf nodes are rectangles. Most of the time, AND nodes are light blue, OR nodes are green, and Leaf nodes are gray.
The color of a node can change, depending on what state it is in. When you select a node, it changes color to yellow. If a node is rolled up (thus hiding all of the subtree beneath it), it changes to pink.
Behavioral Indicators
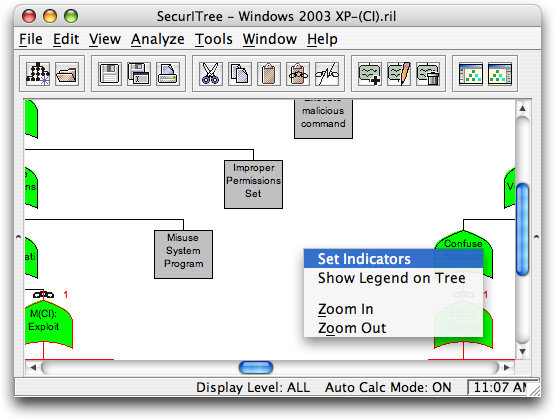
Behavioral Indicators are used as a metric to determine how much an attack costs an adversary, whether it be in resources (money, time, etc.), knowledge (how much technical skill is required), or how much they are willing to risk (what is the chance of getting caught).
To set the indicators that are available for a particular tree, right click on the white background of the tree, and select 'Set Indicators'...
Creating Indicators
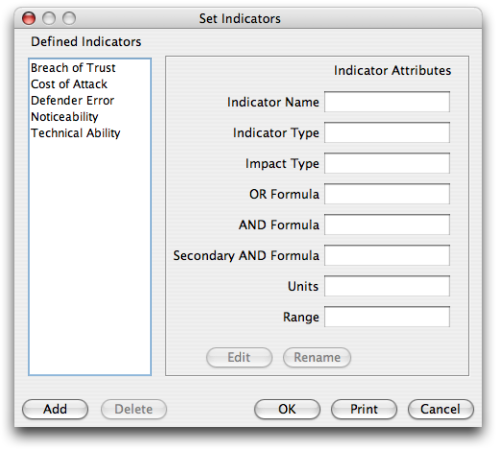
... which will then open a screen which lets you add, edit, or delete indicators for the tree.
Adding Indicators
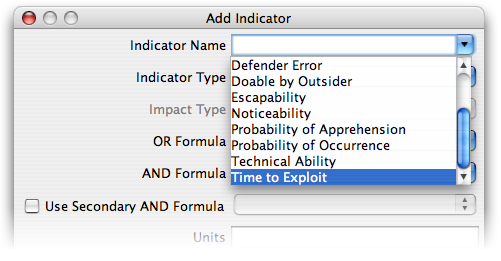
When you click to Add a new indicator, you are presented with a screen showing several dropdown boxes specifying formulae, ranges, etc. There are a number of built-in indicators which you can select from the 'Indicator Name' pulldown. The fields will be populated with the appropriate choices for the indicator you choose.
Using Indicators
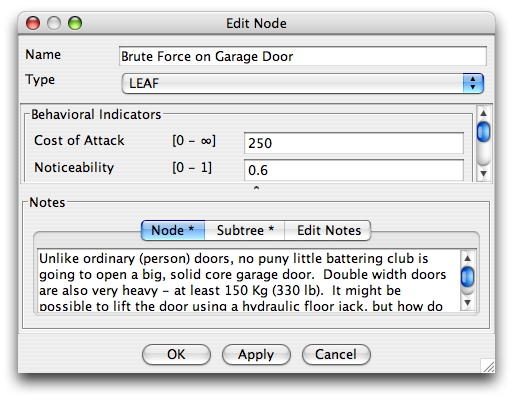
After you have defined the indicators your tree will use, you will need to fill in values for all the leaf nodes. This should be based on an expert's opinion for the values to make any sense. Be sure to document any assumptions that you make in the node notes for future reference.
To set the indicators for a particular node (or to edit other aspects of the node such as its name, node type, associated notes, etc.), you can double-click on the node.
Indicator Scales
In order to compare results between attack trees in a meaningful fashion, you must define a scale for how the resource level equates to the indicator value. For instance, this is an excerpt of the scale of Technical Ability which Amenaza Technologies uses for all of the IT libraries:
- 20: Average User; Can easily surf the Internet, read E-mail, and use Office products.
- 30: Power User; Much more comfortable with computers: comfortable with installing and running new programs. Low programming skills.
- 40: Advanced User; Comfortable with difficult programming. algorithms and theories.
- 80+: God-like status. For all practical reasons, this would be just about impossible.
Viewing Attack Scenarios
By now, we are ready to investigate how many possible attacks can be made on the system. To do this, click on Analysis, then select Attack Scenarios.
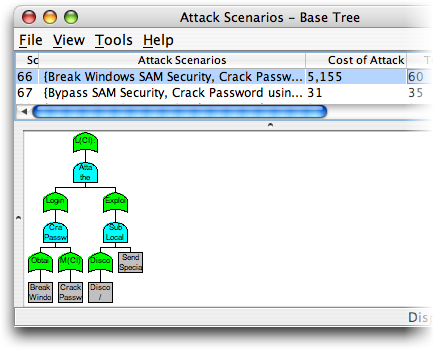
At the top of the window is a list of all possible attacks against the system with the amounts of resources needed to accomplish each one.
If you click on a particular attack, you will see in the lower part of the window a subset of the main tree which describes that particular attack.
The number of scenarios indicates how many ways you can be attacked - in this case, 529.
Analyzing
Viewing attack scenarios on a base tree frequently generates large numbers of potential attacks -- many of which may intuitively seem to be highly improbable. Analytic functions must be applied to reduce the number of attacks to only those that are feasible by the threat agents of interest. In the past, most security analysts have done this intuitively. Unfortunately, intuition can be wrong for a variety of reasons. Even when it is right, it can be difficult for the expert to explain their reasoning to colleagues. SecurITree's analytic functions make the reasoning clear and transparent.
To understand how the analytic functions work, please continue to Introduction to Pruning.
Finished Demonstration
At this point, you should have a decent grasp of how the main functions of SecurITree work. If you want to review the information again, you can hit the Refresh button; if you want to print this demonstration, you can do so using your browser's Print button. Otherwise, please continue on to the next slideshow: Introduction to Pruning, or return to the main demo page.